Hi All
Sorry cannot provide a link but for those unlike Pom who should just read the Abstract and Conclusion the full paper is probably interesting to a little exciting to think what AKIDA with a little Edge Impulse can do. Regards Fact Finder:
Safeguarding Public Spaces: Unveiling Wallet
Snatching through Edge Impulse Technology
Ujjwal Reddy K S
School of Computer Science and Engineering
VIT-AP University
Andhra Pradesh, India
ujjwal.20bci7203@vitap.ac.in
* Kuppusamy P
School of Computer Science and Engineering
VIT-AP University
Andhra Pradesh, India
drpkscse@gmail.com
Abstract—In contemporary society, public space security and
safety are of utmost significance. The theft of wallets, a frequent
type of street crime, puts people’s personal items at risk and
may result in financial loss and psychological misery. By utilizing
Edge Impulse technology to identify and expose wallet-snatching
incidents in public areas, this article offers a fresh solution to
the problem. To develop a reliable and effective wallet-snatching
detection solution, the suggested system blends machine learning
techniques with the strength of the Edge Impulse platform. This
study used Spiking Neural Networks (SNNs) which are inspired
by the biological neural networks found in the brain. Edge
Impulse offers a thorough framework for gathering, prepro-
cessing, and examining data, enabling the creation of extremely
precise machine learning models. The system can accurately
discriminate between legitimate interactions with wallets and
suspicious snatching attempts by training these models on a
dataset that includes both normal and snatching events. The
efficiency of the suggested method is 95% demonstrated by exper-
imental findings, which show high accuracy and low false positive
rates in recognizing wallet snatching instances. Increasing public
safety, giving people a sense of security in public places, and
discouraging prospective wallet-snatching criminals are all goals
of this research.
Index Terms—wallet snatching, public spaces, Edge Impulse,
sensor devices, machine learning, real-time monitoring, security,
privacy
I. INTRODUCTION
Public places are critical for societal interactions and com-
munity participation. They are places of recreation, social-
ization, and public meetings. However, these areas are not
immune to criminal activity, and one typical threat is wallet
snatching. Wallet snatching is the act of forcibly removing
someone’s wallet, which frequently results in financial losses,
identity theft, and psychological suffering for the victims.
Safeguarding public places and combating wallet snatching
necessitate new measures that make use of developing technol-
ogy. In this context, this introduction investigates the potential
of Edge Impulse technology in uncovering and preventing
wallet-snatching events [1].
Wallet-snatching instances can occur in a variety of public
places, including parks, retail malls, congested roadways, and
public transit. These attacks are frequently characterized by
their speed and stealth, giving victims little time to react or
seek aid. Traditional surveillance systems, such as Closed Cir-
cuit Television (CCTV) cameras, have difficulties in efficiently
identifying and preventing wallet-snatching occurrences owing
to variables such as limited coverage, video quality, and human
error in monitoring [2]. As a result, more advanced technical
solutions that can proactively identify and respond to such
situations are required.
Edge Impulse is a new technology that integrates machine
learning algorithms, sensor data, and embedded systems to
generate smart and efficient solutions [3]. It allows machine
learning models to be deployed directly on edge devices such
as smartphones, wearable devices, or Internet of Things (IoT)
devices, reducing the requirement for ongoing access to a
distant server. Edge Impulse is an appropriate solution for
tackling the problem of wallet snatching in public places
because of its capabilities.
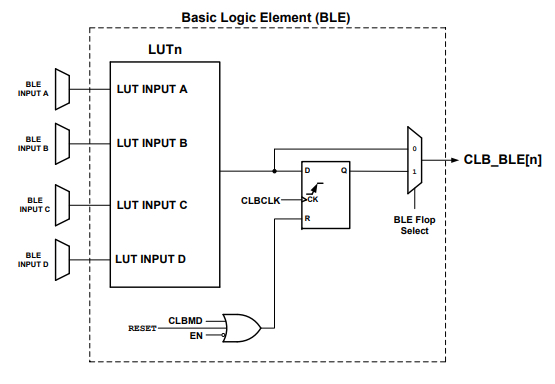
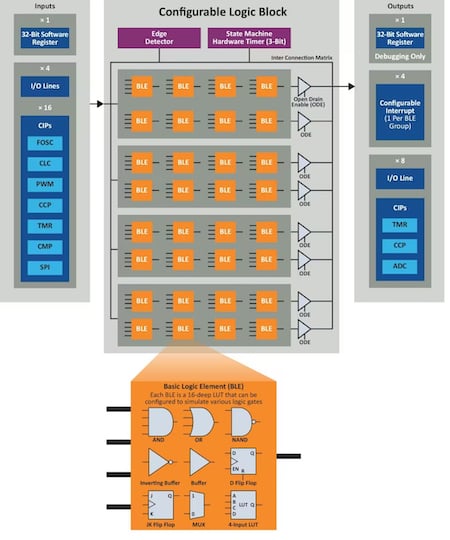
Fig. 1. Edge Impulse Architecture.
It is essential to look into the vast amount of research
and studies done in this specific subject in order to prop-
erly understand the powers of Edge Impulse technology in
revealing instances of wallet theft. Numerous studies have
been conducted to examine the use of computer vision and
machine learning approaches in detecting and preventing crim-
inal activity in public spaces. The topic of utilizing cutting-
edge technologies to improve public safety and security has
been explored in a number of academic studies. This research
has shown how machine learning algorithms may be used
to examine video footage and identify patterns of suspicious
2023 International Conference on Research Methodologies in Knowledge Management, Artificial Intelligence and Telecommunication Engineering (RMKMATE) | 979-8-3503-0570-8/23/$31.00 ©2023 IEEE | DOI: 10.1109/RMKMATE59243.2023.10369744
behavior that could be related to wallet-snatching instances.
These cutting-edge technologies may recognize people who
display suspicious motions or participate in potentially illegal
behaviors by utilizing computer vision techniques, such as
object identification and tracking, enabling proactive interven-
tion. Edge Impulse technology integration has a lot of potential
in this area. It may be trained to recognize certain traits
and attributes linked to wallet snatching through its strong
machine learning skills, improving its capacity to precisely
detect such instances in real-time. Edge Impulse can analyze
trends, spot abnormalities, and notify authorities or security
people to take immediate action by utilizing the enormous
volumes of data gathered from several sources, including
surveillance cameras and sensor networks. The possibility of
predictive analytics to foresee wallet theft episodes based on
previous data and behavioral trends has also been investigated
in this field of research. Machine learning algorithms are
able to recognize high-risk locations and deploy resources
appropriately by examining elements like the time of day,
location, and population density. With the use of this proactive
strategy, law enforcement organizations may deploy people
efficiently and put out preventative measures, which serve to
dissuade prospective criminal activity.
Based on these findings, the use of Edge Impulse technology
in the context of wallet snatching can improve the efficiency of
crime prevention systems [4]. The reaction time may be greatly
decreased by implementing machine learning models directly
on edge devices, enabling real-time detection and fast inter-
vention. Furthermore, Edge Impulse technology can record
and analyze essential data for recognizing wallet-snatching
instances using numerous sensors included in smartphones
or wearable devices, such as accelerometers, gyroscopes, and
cameras.
For example, accelerometer data may be utilized to detect
abrupt movements or violent behaviors that are suggestive of
wallet-snatching attempts [5]. The gyroscope data can offer
information regarding the direction and speed of the grab,
assisting in the tracking of the culprit. Additionally, camera
footage may be analyzed using computer vision algorithms to
detect suspicious activity, identify possible thieves, or collect
photographs for later identification and proof.
The increasing availability of data can further benefit the use
of Edge Impulse technology in wallet snatching prevention.
With the growth of smartphones and wearable devices, there is
an abundance of sensor data that can be gathered and analyzed
in order to create strong machine learning models. This data
may be used to train algorithms to recognize certain patterns or
abnormalities related with wallet-snatching instances, boosting
the system’s accuracy and dependability.
Furthermore, integrating Edge Impulse technology with
current surveillance systems can improve their capabilities.
A complete and intelligent system may be constructed by
integrating the strengths of both technologies, such as the
extensive coverage of CCTV cameras and the real-time anal-
ysis of edge devices. This integrated strategy would allow for
proactive identification and rapid reaction to wallet-snatching
occurrences, minimizing the impact on victims and discour-
aging future perpetrators.
Finally, wallet snatching in public places is a serious danger
to public safety and individual well-being [6]. Innovative
techniques are necessary to overcome this difficulty, and Edge
Impulse technology has intriguing possibilities. Edge Impulse
provides real-time detection and fast action in wallet snatching
occurrences by employing machine learning models installed
directly on edge devices. It captures and analyses pertinent
information using multiple sensors and data sources accessible
on smartphones and wearable devices. Integrating Edge Im-
pulse technology with current monitoring systems can improve
the efficacy of crime prevention efforts. These developments
can help to protect public places and expose wallet snatching,
resulting in safer and more secure communities.
A. Motivation
This study aims to use the potential of Edge Impulse
technology to make public areas safer for citizens by efficiently
fighting wallet-snatching events. We hope that by finding a
solution, we can contribute to the wider objective of protecting
public places and improving the general quality of life in our
communities.
B. Contribution
• The study presents an innovative use of Edge Impulse
technology for improving public safety.
• This study proposed SNNs.
• The created machine learning model detects wallet-
snatching episodes in public places with high accuracy
and efficiency.
II. RELATED WORK
The study proposes a framework comprised of two major
components: a behavior model and a detection technique [7].
The behavior model captures the software’s valid behavior
by monitoring its execution and gathering information about
its interactions with the system and the user. The detection
method compares the observed behavior of a software instance
to the behavior model to discover any differences that signal
probable theft. The authors conducted trials with real-world
software applications to assess the efficacy of their technique.
They tested their system’s detection accuracy, false positive
rate, and false negative rate. The results indicated promising
performance in detecting software theft occurrences properly
while keeping false alarms to an acceptable level. The study
presents an overview of the many processes involved in
the identification of anomalous behavior, including human
detection, feature extraction, and classification [8]. It em-
phasizes the importance of Convolutional Neural Networks
(CNNs) in dealing with the complexities of visual input and
extracting important characteristics for behavioral research.
Furthermore, the authors explore several CNN architectures
used for anomalous behavior identification, such as AlexNet,
Visual Geometry Group Network (VGGNet), and Residual
Neural Network (ResNet) [9]–[11]. They also investigate the
use of various datasets and assessment criteria in evaluating
the performance of these models. The survey includes a wide
range of applications where aberrant behavior identification is
critical, such as crowd monitoring, public space surveillance,
and anomaly detection in industrial settings [8]. The authors
assess the merits and limits of existing approaches, as well as
new research avenues and opportunities for development.
The suggested technique consists of two major steps: feature
engineering-based preprocessing and energy theft detection
using gradient boosting [12]. Various characteristics from
the electricity usage data are extracted during the feature
engineering-based preprocessing stage. These traits are in-
tended to detect trends and behaviors that may suggest possible
energy theft. After preprocessing the data, the authors use
gradient boosting, a machine learning approach, to detect
energy theft. Gradient boosting is an ensemble learning ap-
proach that combines numerous weak predictive models to
build a strong predictive model. It constructs decision trees in
a sequential manner, with each succeeding tree learning from
the mistakes of the preceding ones. The suggested strategy
is evaluated by the authors using real-world power use data.
They compare their approach’s performance to that of other
current approaches for detecting energy theft, such as decision
trees, random forests, and support vector machines [13]–
[15]. Accuracy, precision, recall, and F1-score are among the
assessment criteria employed. The paper’s results show that
the suggested technique beats the other methods in terms
of energy theft detection accuracy. The authors credit this
enhanced performance to the preprocessing stage based on
feature engineering and the efficiency of gradient boosting in
identifying complicated connections in the data.
The study is primarily concerned with analyzing power
use trends and discovering abnormalities that might suggest
theft [16]. The system learns to discern between regular use
patterns and suspicious actions that signal theft by training the
decision tree and Support Vector Machine (SVM) models on
historical data. The attributes chosen are used to categorize
incidents as either theft or non-theft. The suggested technique
is tested using real-world smart grid data. The findings show
that the decision tree and SVM-based methods can identify
theft in smart grids with high accuracy and low false positive
rates. The study focuses on identifying instances of theft by
collecting temporal relationships in energy use data [17]. The
system learns to recognize regular consumption patterns and
detect variations that suggest theft by training the CNN-Long
Short-Term Memory (LSTM) model on historical data. The
suggested method is tested using real-world smart grid data,
and the findings show that it is successful at identifying power
theft [18]. The CNN-LSTM-based technique beats existing
approaches in terms of detection accuracy. Both papers address
the important issue of theft detection in smart grid systems,
but they employ different techniques [16], [17]. The first
paper utilizes decision trees and SVM for feature selection
and classification, while the second paper employs CNNs and
LSTM networks for feature extraction and anomaly detection.
These approaches contribute to the development of effective
methods for enhancing the security and reliability of smart
grid systems.
The study most likely proposes an algorithm or strategy
that employs computer vision and motion analysis techniques
to detect suspicious or illegal behavior in video footage [19].
The suggested approach most likely seeks to discriminate
between routine activities and probable criminal behaviors
by analyzing the motion patterns of humans or items in a
setting [20]. It is difficult to offer a full description of the
methodology, results, or conclusions of the study based on
the information supplied. However, it may be deduced that the
authors suggest a way for developing an automated criminal
detection system that combines motion analysis with intel-
ligent information-concealing strategies. The authors suggest
a chain-snatching detection safety system that detects and
prevents chain-snatching accidents by utilizing sophisticated
technologies [21]. However, without complete access to the
article, it is difficult to offer extensive information regarding
the system’s methodology, components, or methods used. To
detect rapid and strong movements associated with chain
snatching attempts, the system is likely to include various
sensors such as motion sensors or accelerometers. Image
processing methods may also be used to identify possible
chain snatchers or to collect photographs of the occurrence
for additional investigation or proof [22]. In addition, when a
chain-snatching incident is identified, the system might contain
an alarm or notification mechanism that warns surrounding
persons or authorities in real time. This quick reaction can
dissuade offenders while also providing urgent support to
victims. The report will most likely offer experimental findings
and assessments to assess the suggested system’s usefulness
in effectively identifying chain-snatching occurrences while
minimizing false alarms [21]. It may also address the system’s
weaknesses, prospective areas for development, and future
research directions in this subject.
The document most likely presents a proposed approach or
algorithm for detecting snatch stealing [23]. It may describe
the selection and extraction of low-level video data elements
such as motion analysis, object tracking, or other relevant
information that can be utilized to detect snatch-snatching
instances. The authors may have also investigated various
strategies for identifying and discriminating between regular
and snatch-stealing incidents. Given that the paper was deliv-
ered in 2010, it is crucial to highlight that the material provided
in it is based on research and technology breakthroughs
accessible at the time [23]. It’s probable that recent advances in
computer vision, machine learning, and surveillance systems
have pushed the area of snatch-steal detection even further.
The authors present an action attribute modeling technique
for automatically recognizing snatch-stealing incidents [24].
To identify possible snatch-steal instances, the technique en-
tails analyzing the activities and characteristics displayed by
persons in surveillance recordings. The idea is to create a
system that can send real-time alerts to security workers or
law enforcement organizations in order to assist avoid such
crimes or respond promptly when they occur. The document
most likely outlines the methods and algorithms used to
detect snatch-stealing occurrences, including the extraction of
key characteristics, training a model using labeled data, and
evaluating the suggested solution. It might also go through
the datasets used for training and testing, as well as the
performance measures used to assess the system’s efficacy.
Because the study was published in 2018, it is crucial to
highlight that advances in the area may have occurred since
then, and other methodologies or approaches may have been
created [24].
The study describes the integrated framework’s many com-
ponents, such as data collecting, preprocessing, feature extrac-
tion, and crime detection [25]. In addition, the authors give
experimental results based on real-world data to illustrate the
efficacy of their technique. The results show that the suggested
framework may detect tiny crimes in a fast and accurate
manner, allowing law enforcement authorities to respond more
efficiently. The research focuses on the use of deep learning
algorithms to detect trustworthy human suspicious conduct
in surveillance films [26]. By using the capabilities of deep
learning algorithms, scientists hope to increase the accuracy
and reliability of suspicious behavior detection. The study
provides a full description of the suggested technique, which
includes surveillance video preprocessing, feature extraction
with CNNs, and categorization of suspicious actions with
Recurrent Neural Networks (RNNs) [27], [28]. The authors
also explore the difficulties connected with detecting sus-
picious behavior and provide strategies to overcome them.
The research focuses on the cap-snatching mechanism used
by the yeast L-A double-stranded Ribonucleic Acid (RNA)
virus [29]. The cap-snatching mechanism is a technique used
by certain RNA viruses to hijack the host’s messenger RNA
(mRNA) cap structure for viral RNA production. The authors
study the particular cap-snatching method used by the yeast
L-A double-stranded RNA virus and give deep insights into
its molecular processes. They investigate the viral variables
involved in cap-snatching and their interplay with host factors.
The authors’ research contributes to the knowledge of RNA
virus viral replication techniques and sheds insight on the
complicated mechanisms involved in the reproduction of the
yeast LA double-stranded RNA virus [29]. The findings of
this study are useful for virology research and increase our
understanding of viral replication techniques.
Continued in next post......